Security issues took a turn for the serious in 2017. This time around we still suffered the password breaches, malware annoyances, and stolen credit card numbers that have become commonplace in recent years. But the headlines were dominated by more sobering issues.
We saw foreign adversaries trying to infiltrate critical infrastructure; major U.S. government hacking tools exposed; a major breach that called into question the use of social security numbers as identification; the U.S. government turning negative towards online user privacy; and popular consumer software dragged into the world of corporate and state espionage.
Whew. It was a big year for computer security, and some of 2017’s events will no doubt reach well into 2018 and beyond. Let’s take a look.
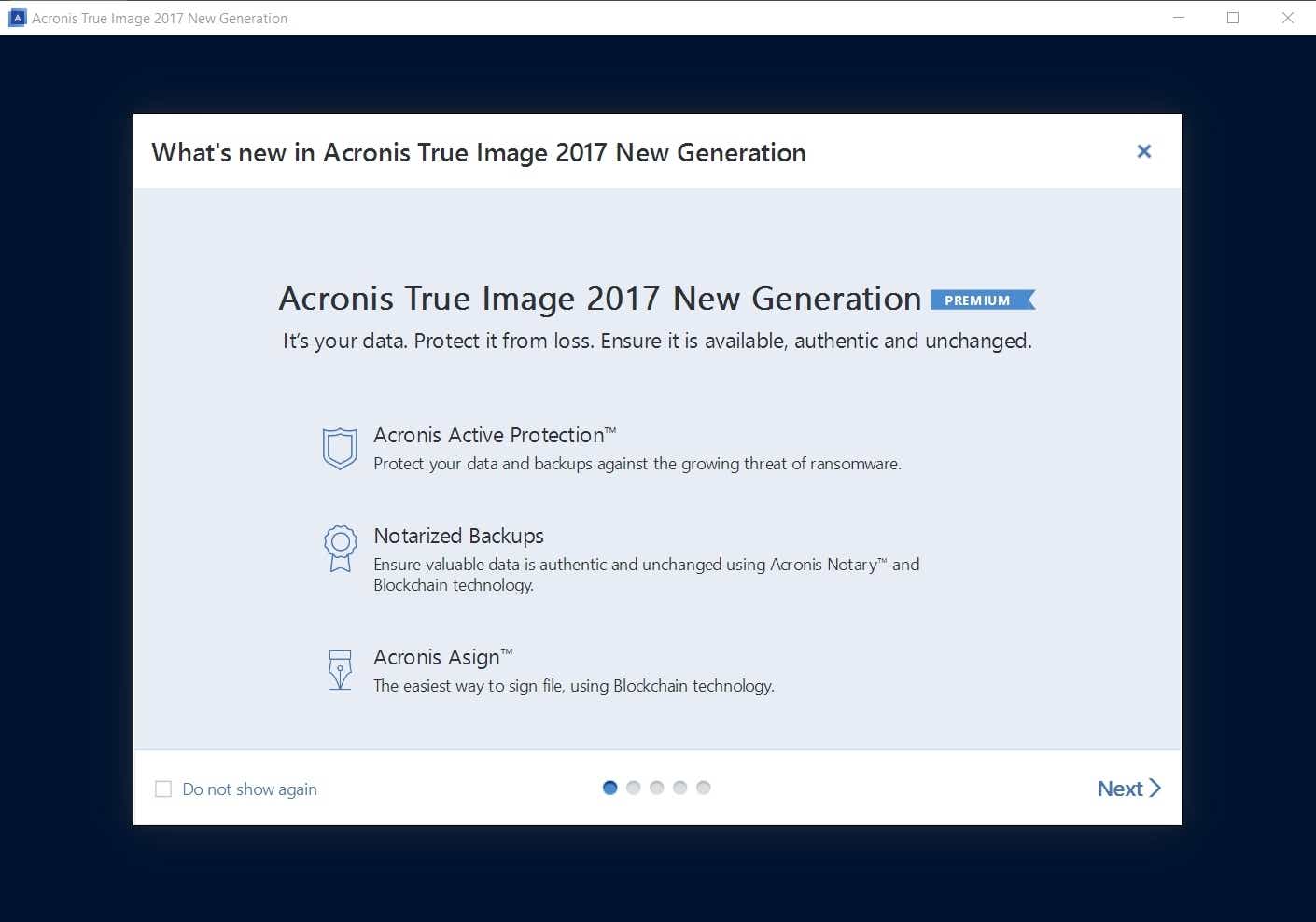
Shadow Brokers and Vault7 leaks
 Wikileaks
Wikileaks
A CIA logo released by Wikileaks as part of Vault7.
Two of the defining computer security events of 2017 were leaks that exposed closely held hacking secrets of the U.S. government. Wikileaks got the ball rolling in March with the release of its so-called ”Vault7” leaks revealing what appeared to be a cache of computer vulnerabilities and operating methods used by the Central Intelligence Agency to infiltrate target devices.
Then in April the Shadow Brokers—an anonymous group of hackers that first came to notoriety in 2016—released a trove of attack tools linked to the National Security Agency.
Both releases would have significant impacts on computer device security.
Equifax Breach
“Jaw-dropping” does not begin to describe the Equifax breach, which came to light in September. Equifax is one of the three major consumer credit reporting agencies in the United States. The hackers struck in the spring, seizing 143 million Social Security numbers—that’s more than half of the U.S. population. A failure to install current security patches on its network opened the door to the attack, the company said. Despite the devastating hack Equifax still won an anti-fraud contract from the Internal Revenue Service, though it was later suspended.
ISP tracking rules
 Bill Koplitz/FEMA
Bill Koplitz/FEMA In late March, Congress decided to remove the privacy rules passed by the Federal Communications Commission in 2016. The rules had not yet come into effect when they were dumped, but they would have required opt-in permission from broadband customers before ISPs could use their personal information and browsing habits for marketing or analytics purposes.
Republicans said the rules unfairly hamstrung Internet Service Providers, while major Internet companies could collect and use all the personal data they wanted. What that argument ignores, however, is that ISP data collection is much harder to mitigate since it controls the very wires and cables you need to get online. Plus, few people are particularly pleased that Facebook and Google have free reign, either.
CCleaner gets a backdoor
In September, security researches at Cisco Talos discovered malicious code buried inside CCleaner, a popular Windows PC utility. The malware was designed to steal personal data from infected machines. Avast added to the intrigue when it discovered that there was a second stage to the malware for infected machines in specific companies such as Cisco, Sony, and HTC. Presumably, the malware was looking to steal company secrets in those organizations. All in all around two million people were believed to be affected by the corrupted versions of CCleaner. The malware has since been removed from the latest versions of the software.
[ Further reading: The best antivirus for Windows PCs ]
Kaspersky controversy
 David Orban via Flickr
David Orban via Flickr If there’s a headline-grabbing computer security controversy of 2017, it has to be the allegation that Kasperksy Anti-virus products are a spying tool for Russian intelligence. In October, The Wall Street Journal said hackers working for the Russian government used Kaspersky Anti-Virus to identify and target a National Security Agency contractor in order to steal American hacking secrets.
Kaspersky vigorously denied the claims and said the contractor caused the leak by running Kasperksy on a home machine that contained weaponized malware. To help allay fears, Kaspersky announced it would allow third-parties to audit its code—a measure that some experts argue doesn’t go far enough. As a result of the reports, and bans of Kaspersky products by the government, Kaspersky’s Washington DC office shut down in December, the contractor who brought U.S. hacking secrets home in the first place plead guilty to taking classified documents, and Kaspersky sued the Department of Homeland Security over blacklisting its products.
Game of Leaks
It’s not easy being a fount of popular TV shows—especially when everyone wants to know what you have planned. HBO found that out the hard way in July when hackers claimed to have purloined 1.5 terabytes of data from the pay TV channel. Among the stolen cache were management emails, upcoming episodes for popular HBO shows, and draft scripts of one Game of Thrones episode that had not yet been aired. In November, U.S. law enforcement charged an Iranian hacker with the data theft. As for HBO, now it understands that when it comes to computer security you win or you leak.
Yahoo’s 2016 hacks gets worse
 Yahoo
Yahoo
Yahoo’s headquarters in Sunnyvale, California.
Oh boy. Before Yahoo was absorbed into Verizon the Internet giant endured a massive hack exposing usernames and passwords. In fact, it was a record-breaking hack twice over in 2016, but even that wasn’t the end of the saga.
The company recently amended the number of Yahoo accounts affected by the data breach dating from 2013. By the end of 2016, that number was believed to be one billion accounts, but in October Yahoo updated that number to three billion. Basically, if you had a Yahoo account at any time in 2013, your username and password leaked, once again driving home the importance of using unique passwords for every website.
[ Further reading: The best password managers ]
Ransomware makes you WannaCry
 Malwarebytes
Malwarebytes In May, a piece of ransomware called WannaCry made a second appearance after first rearing its head in March. The May attacks were more problematic since WannaCry included a “worm-like component” that helped spread the malware.
That component was particularly notable since it was derived from an exploit called EternalBlue that was part of the ShadowBrokers leaks in April. The WannaCry attack was so successful because the EternalBlue exploit had either not been patched in a timely manner on infected machines, or the machines were too outdated to receive exploit patches. The WannaCry infection was so pernicious that Microsoft released patches for Windows XP, Windows Server 2013, and Windows 8. The ransomware was eventually halted in May when British security researcher Marcus Hutchins inadvertently discovered a kill switch for the malware.
EternalBlue would also appear in NotPetya, another piece of notable ransomware that grabbed headlines in 2017.
[ Further reading: How to rescue your PC from ransomware ]
Cloudbleed
 Cloudflare
CloudflareContent Delivery Network Cloudflare ended up with a significant bug in Feburary 2017 that affected the way the company parsed HTML. The company often takes regular HTTP webpages from its client websites and turns them into the more secure HTTPS pages. The parser can also carry out tasks such as hiding content from bots, hiding email addresses, and working with Google’s AMP system.
But the parser system also had a flaw that could potentially leak sensitive information some of which was cached by search engines such as Bing and Google. That sensitive information included items like private messages from dating sites, text chats from popular messaging services, password manager data, and hotel bookings.
While the technical causes were different, the results of the Cloud Flare bug were similar to the Heartbleed bug from 2014.
Voters exposed
 Thinkstock
ThinkstockServers are tricky things. Not only do they have to be patched to keep the bad guys out, but you also have to be careful of misconfigurations that expose private data.
A data firm called Deep Root Analytics found that out in June when one of its Amazon S3 servers was misconfigured and exposed the personal information for 198 million voters, according to Wired. The misconfigured server was discovered by a security analyst, and presumably the data never fell into malicious hands. Even if it had, the risk might have been minimal. Wired noted in a follow-up report that most of the personal data exposed in the flaw could also be accessed from public records.
HP laptops with keyloggers
 Magdalena Petrova
Magdalena Petrova For HP, 2017 was the year of the keylogger. It all started in May when a Swiss security firm discovered that more than two dozen “HP laptop models were recording users’ keystrokes.” The keylogging software was in the PC’s audio driver existing since at least 2015. The driver was supposed to be alerted when a particular key on the PC was hit, but to do that the driver was capturing all keystrokes. Those keystrokes were also stored in an unencrypted file. Potentially exposing passwords, usernames, and private correspondence should the user get hacked.
More recently in December, another security researcher found a keylogger in the Synaptics touchpad driver for nearly 500 models of HP notebooks going back to 2012. Luckily, the December keylogger was disabled by default, and in both cases the installation of the keylogger appeared to be either inadvertent or a mistake.
Power outage Ukraine
In January 2017, security researchers concluded that hackers caused a power outage in Ukraine during December 2016—one of the country’s coldest months. This was the second time a ‘cyber attack’ had triggered a power outage in the country.
Power outage hacks sound scary and bring up the obvious question of whether they could happen in the U.S. The answer to that is yes, it could. In fact, attacks against American infrastructure have already happened. In mid-December, Reuters reported that hackers had broken into the safety system of an unnamed “critical infrastructure facility.” Before that, in September, Symantec warned that foreign hackers were actively targeting European and American energy facilities, and is some cases had operational access, as reported by Reuters. And oh, yeah, hackers are also targeting American nuclear facilities.
Happy New Year!