(Editor’s Note: Intel has now provided a list of the affected processors, as well as when it first learned of the problem.) Intel said Thursday that by next week, the company expects to have patched 90 percent of its processors that it released within the last five years, making PCs and servers “immune” from both the Spectre and Meltdown exploits, the company said.
Intel’s announcement was the latest update in an ongoing fight to patch microprocessors against a pair of vulnerabilities released this week. The company said that it had already released updates “for the majority” of its chips released in the last five years, and would hit the 90 percent mark next week. The updates are being released as firmware updates and software patches.
Right now, there are two areas of concern for the Spectre and Meltdown vulnerabilities, which we’ve described in more detail in a separate FAQ. First, there’s the security concerns: both vulnerabilities allow an attacker to peer into privileged data that normally is concealed. There’s also a worry that any patches will slow down PCs as a result, though Intel has maintained that the average user will be only slightly affected.
What this means: At this point, we know that major chip and operating system vendors are aware of the problem and working to release fixes. The first should probably arrive as part of Microsoft’s Patch Tuesday, or earlier. What’s unclear is how many different types of software and CPU architectures the patches will affect, and the amount of performance (if any) that PCs will suffer as a result. It’s a very complicated issue, so we’ve created an Intel CPU kernel bug FAQ that breaks down all the info we know in clear, easy-to-read language to help you wrap your head around it.
How we got here
If you think both Spectre and Meltdown were new to Intel — no, they’re not. In a FAQ published Thursday, Intel said it was aware of the problem in June 2017. “In this case, the security researchers presented their findings in confidence, and we and other companies worked together to verify their results, develop and validate firmware and operating system updates for impacted technologies, and make them widely available as rapidly as possible,” the company said.
During a conference call Wednesday afternoon, Intel shed more light on the CPU kernel vulnerability, now being referred to as a “side channel analysis exploit.” Expect to see patches roll out to address the flaw over the next several weeks, Intel executives said. The performance impact of the patches is expected to be at frustrating levels—somewhere between 0 and 30 percent, though “average” PC users are expected to see little impact.
To the question of which Intel microprocessors are affected: it’s pretty much all of them. Here’s the complete list, as published by Intel.
- Intel Core i3 processor (45nm and 32nm)
- Intel Core i5 processor (45nm and 32nm)
- Intel Core i7 processor (45nm and 32nm)
- Intel Core M processor family (45nm and 32nm)
- 2nd generation Intel Core processors
- 3rd generation Intel Core processors
- 4th generation Intel Core processors
- 5th generation Intel Core processors
- 6th generation Intel Core processors
- 7th generation Intel Core processors
- 8th generation Intel Core processors
- Intel Core X-series Processor Family for Intel X99 platforms
- Intel Core X-series Processor Family for Intel X299 platforms
- Intel Xeon processor 3400 series
- Intel Xeon processor 3600 series
- Intel Xeon processor 5500 series
- Intel Xeon processor 5600 series
- Intel Xeon processor 6500 series
- Intel Xeon processor 7500 series
- Intel Xeon Processor E3 Family
- Intel Xeon Processor E3 v2 Family
- Intel Xeon Processor E3 v3 Family
- Intel Xeon Processor E3 v4 Family
- Intel Xeon Processor E3 v5 Family
- Intel Xeon Processor E3 v6 Family
- Intel Xeon Processor E5 Family
- Intel Xeon Processor E5 v2 Family
- Intel Xeon Processor E5 v3 Family
- Intel Xeon Processor E5 v4 Family
- Intel Xeon Processor E7 Family
- Intel Xeon Processor E7 v2 Family
- Intel Xeon Processor E7 v3 Family
- Intel Xeon Processor E7 v4 Family
- Intel Xeon Processor Scalable Family
- Intel Xeon Phi Processor 3200, 5200, 7200 Series
- Intel Atom Processor C Series
- Intel Atom Processor E Series
- Intel Atom Processor A Series
- Intel Atom Processor x3 Series
- Intel Atom Processor Z Series
- Intel Celeron Processor J Series
- Intel Celeron Processor N Series
- Intel Pentium Processor J Series
- Intel Pentium Processor N Series
Intel, whose processors were the focus of an initial report from The Register, said that both ARM and AMD, as well as several operating system vendors, have been notified of the vulnerability. The flaw was first discovered by Google’s Project Zero security team, says Intel, which Google confirmed. Two names, Spectre and Meltdown, are also being used to identify the vulnerabilities.
Intel said that it would issue its own microcode updates to address the issue, and over time some of these fixes will be rolled into hardware. At press time, Microsoft declined to comment on how it would proceed, though it is expected to release its own patches soon. Google, too, issued its own report on which of its products could be affected: These include Chrome and Android phones, though the latter will depend on how quickly phone makers roll out updates.
What is a side-channel analysis exploit?
According to Intel, the exploit is a way for an attacker to observe the content of privileged memory, exploiting a CPU technique called speculative execution to circumvent expected privilege levels. That can give an attacker access to data it normally wouldn’t, though Intel has said that the data won’t be deleted or modified.
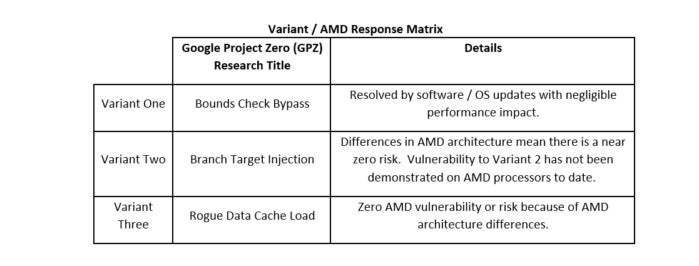
In fact, Intel and the researchers identified three variants, known as a “bounds check bypass,” “branch target injection,” and a “rogue data load,” all of which used slightly different methods of attack. In each case, operating-system updates mitigated the problem.
Steve Smith, one of the engineering leads at Intel who reported the company’s findings, added that no attacks using the vulnerability has been discovered in the wild. He also denied reports that the vulnerability was a flaw, or that it was specific to Intel. “The processor is in fact operating as we designed it,” Smith told investors during the conference call.
The discovery led to hardware makers around the world responding to the vulnerability in a “responsible manner,” Smith said.
Intel: this is an industry-wide problem
The companies had planned to make the disclosure next week when the patches became available. Intel said it was commenting in advance because of what it called “current inaccurate media reports,” though nothing in its statement denied those reports. The company released a statement to the media, then followed up with a conference call.
“Intel and other technology companies have been made aware of new security research describing software analysis methods that, when used for malicious purposes, have the potential to improperly gather sensitive data from computing devices that are operating as designed,” Intel said. “Intel believes these exploits do not have the potential to corrupt, modify or delete data.”
Intel maintained that the vulnerability is tied to other architectures beyond its own, naming AMD—which denied that its chips are affected—as well as ARM Holdings, the architecture at the heart of most smartphone processors—as additional companies whose products are “susceptible” to these exploits, along with several operating system vendors.
“We’re aware of this industry-wide issue and have been working closely with chip manufacturers to develop and test mitigations to protect our customers,” a Microsoft spokesperson said in an email. “We are in the process of deploying mitigations to cloud services and have also released security updates to protect Windows customers against vulnerabilities affecting supported hardware chips from Intel, ARM, and AMD.”
For its part, AMD denied that its processors were affected, stating that there was a “near zero risk to AMD processors” at this time. The company also outlined its responses to the three variants of the vulnerability in a graphic.
 AMD
AMDIntel sought to explain why it hadn’t yet revealed the vulnerability, claiming it was close to having done so before the news broke. “Intel is committed to the industry best practice of responsible disclosure of potential security issues, which is why Intel and other vendors had planned to disclose this issue next week when more software and firmware updates will be available,” Intel said.
Google also reported that its Chrome browser is affected, though there’s a two-step cure: first, make sure that your browser is updated up to version 63. Second, an optional feature called Site Isolation can be enabled to provide mitigation by isolating websites into separate address spaces. This optional flag, which can be turned on at chrome://flags/#enable-site-per-process, turns on Site Isolation. Finally, Chrome 64, which will be released on Jan. 23, will protect users against the side-channel exploit, Google said.
Mozilla said is adjusting its timing within Firefox to mitigate the effects of the two vulnerabilities.
What can you do in the meantime? Intel’s advice is to follow the age-old mantra of patch, patch, patch. “Check with your operating system vendor or system manufacturer and apply any available updates as soon as they are available,” the company said. “Following good security practices that protect against malware in general will also help protect against possible exploitation until updates can be applied.”
The performance issue: will a patch slow your PC down?
But with a patch, is the cure worse than the disease? According to The Register, which originally reported the story, PC users could be “looking at a ballpark figure of five to 30 percent slow down, depending on the task and the processor model” if a patch is applied.
Intel seems to feel that the typical end user won’t suffer any ill effects. “Contrary to some reports, any performance impacts are workload-dependent, and, for the average computer user, should not be significant and will be mitigated over time,” Intel said in its statement.
Intel went a bit further on its call, but again without any of the real clarity customers may have hoped for. “It depends on the workload specifically in use,” Smith said.
Intel doesn’t differentiate between client PCs and datacenter servers when looking at the effects of the bug, executives said. Instead, those applications which exist primarily in the user space could see an impact of between 0 and 2 percent, executives said. But synthetic workloads, which lean heavily on the interaction between the application and the operating system, could suffer up to a 30 percent performance hit.
More evidence suggests that PC users won’t feel any significant effects from a patch. As our earlier report indicated, tests on several popular games using a patched version of Linux—not Windows—didn’t indicate any frame-rate drops outside a margin of error. The games tested included Dota 2, Counter-Strike: Global Offensive, Deus Ex: Mankind Divided, Dawn of War III, F1 2017, and The Talos Principle on a Linux 4.15-rc6 machine with a Core i7-8700K and Radeon Vega 64.
None of those ran on Microsoft’s DirectX technology though, which integrates deeply with the Windows operating system.
Check back with PCWorld for upcoming reports, and see our updated FAQ for a summary of the latest findings.
This story was updated at 3:36 PM on Jan. 4 with additional details from Intel on which processors are affected.
